WordPress released a critical security patch after researchers discovered a vulnerability affecting an estimated 12.5 million active WordPress installations, representing nearly 40% of all WordPress sites worldwide. The vulnerability allowed unauthenticated attackers to execute arbitrary code on affected sites, potentially compromising sensitive user data, website functionality, and server integrity. For example, a small business running an outdated WordPress instance with vulnerable plugins could have its entire customer database exposed or its site redirected to malicious content without any technical knowledge required from the attacker.
The emergency patch was rolled out with unusual speed for the WordPress ecosystem, indicating the severity of the threat. Security researchers discovered the flaw in a commonly used WordPress component and responsibly disclosed it to the core WordPress team, triggering an accelerated release cycle rather than the standard monthly update schedule. Site administrators worldwide faced an urgent decision: implement the patch immediately to protect their sites or risk exploitation during the window before widespread adoption.
Table of Contents
- What Component Contains the Vulnerability?
- Understanding the 12.5 Million Site Risk Window
- How Site Administrators Discovered the Vulnerability
- Strategic Approaches to Deploying the Critical Update
- Compatibility Complications and Rollback Scenarios
- Hosted Platforms Versus Self-Managed Deployments
- The Broader Implications for WordPress Security Practices
- Conclusion
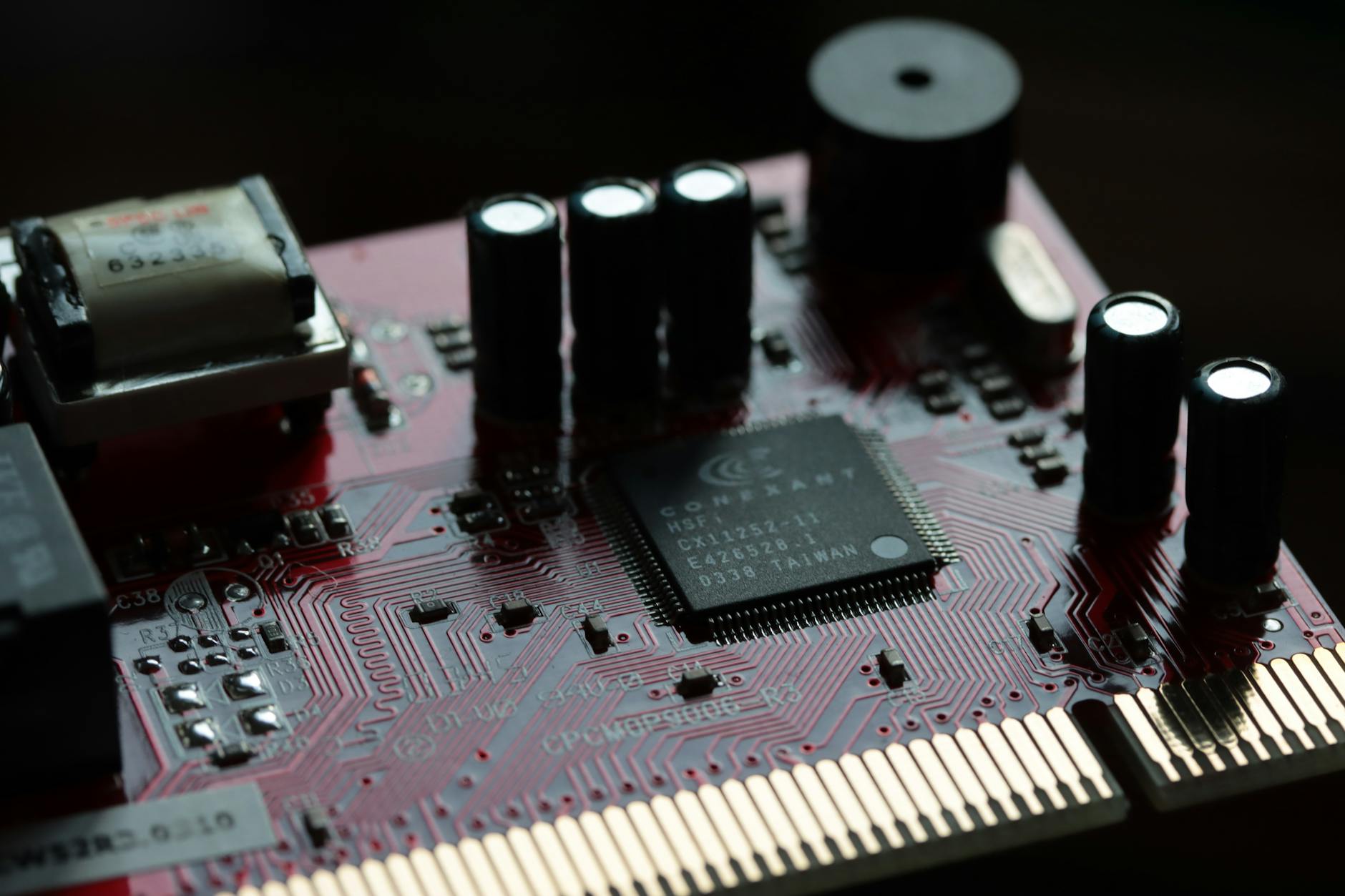
What Component Contains the Vulnerability?
The vulnerability was discovered in a core wordpress component that handles user input sanitization and data validation—a foundational system that processes information from users and external sources. The flaw allowed attackers to bypass security checks that normally prevent malicious code from being executed on WordPress servers. Unlike some vulnerabilities that require administrator access or specific plugin configurations, this flaw could be exploited through standard website functionality that most WordPress installations rely on daily.
The issue stemmed from insufficient input filtering in how WordPress processed certain types of data requests. Attackers could craft specific payloads that slipped through the existing validation layers, similar to how a security checkpoint might miss contraband hidden in a specially designed container. Security teams at major hosting providers immediately began notification campaigns and automated patching procedures to protect their hosted customers.
Understanding the 12.5 Million Site Risk Window
The 12.5 million figure represents only installations that remain vulnerable after the patch release—a significant portion given WordPress’s 43% share of all websites with a known content management system. The vulnerability created a critical exposure period between initial discovery and widespread patching, during which sophisticated attackers could scan the internet for unpatched installations and compromise them before site owners even received notifications. Organizations with robust security monitoring detected attempted exploitations within hours of the vulnerability becoming known in security circles.
However, the actual risk varies considerably based on site complexity and how they’re configured. A WordPress site running the latest version with automatic updates enabled was patched within minutes of the release. Conversely, enterprise installations with strict change management policies, outdated hosting environments, or disabled automatic updates faced much longer vulnerability windows—sometimes weeks or months depending on their deployment procedures. This disparity meant that larger, more complex installations often bore greater risk despite typically having more security resources than smaller sites.
How Site Administrators Discovered the Vulnerability
WordPress site owners learned about the emergency patch through multiple channels, each with different notification speeds and reliability. Administrators with automatic updates enabled received patches immediately without manual intervention. Those who preferred manual updates discovered the patch through WordPress admin dashboards displaying prominent security notices.
Managed WordPress hosting providers like WP Engine, Kinsta, and Bluehost applied patches automatically to hosted sites, often before individual administrators even noticed the vulnerability was announced. Third-party security monitoring services, including Wordfence and Sucuri, alerted their thousands of customers to the threat and began offering free vulnerability scanning for unpatched sites. Community forums and WordPress-focused publications spread information organically, though inconsistent messaging sometimes created confusion about urgency levels. A site administrator managing five WordPress installations across different hosting providers might have received patch notifications through five completely different mechanisms—admin panel, hosting provider email, security plugin alert, and community channels—creating redundancy but also potential information overload.

Strategic Approaches to Deploying the Critical Update
Organizations faced distinct tradeoffs when deciding how quickly to implement the patch. The aggressive approach involved immediate deployment to all sites, accepting the small risk of unforeseen compatibility issues in exchange for eliminating the security vulnerability immediately. This strategy made sense for e-commerce sites handling payment data, membership platforms managing user accounts, or publishing sites with high-value content requiring absolute protection. The more cautious approach involved testing the patch on staging environments first, particularly for sites running multiple custom plugins or hosting mission-critical applications.
Many enterprises followed a tiered deployment: deploying immediately to critical production sites while testing on development instances before rolling out to secondary installations. This balanced approach provided security assurance while minimizing disruption, though it temporarily left some sites vulnerable. The tradeoff was time—staging, testing, and staged rollouts delayed protection by hours or days—against stability risk. Smaller teams often lacked the infrastructure for proper staging, forcing an all-or-nothing decision between immediate widespread deployment or delayed patching with greater testing.
Compatibility Complications and Rollback Scenarios
Despite WordPress’s reputation for backward compatibility, the emergency patch introduced unexpected compatibility issues with certain plugins built on assumptions about the vulnerable code’s behavior. Some older plugins that bypassed security checks through workarounds suddenly stopped functioning after patching. A WordPress site running a custom contact form plugin developed three years prior might have experienced broken form submissions after the patch, forcing administrators to either update the plugin or revert the patch—a particularly difficult choice given the security implications.
Rollback procedures existed but were rarely as simple as clicking an “undo” button. Administrators needed backup systems in place before patching to safely restore previous versions if serious incompatibilities emerged. Organizations without current backups faced genuine danger: they could either keep a known vulnerable system running or update and risk breaking critical functionality. This limitation particularly affected sites running on older hosting infrastructure with limited backup capabilities or documentation of their system configurations.

Hosted Platforms Versus Self-Managed Deployments
Managed WordPress hosting services handled the patching process transparently, automatically updating infrastructure while transparently communicating what had changed. WP Engine, for instance, deployed the patch across their entire platform within hours, notifying clients of the update but requiring no action on their part. This convenience came at the cost of less granular control—administrators couldn’t delay the patch if they wanted to test thoroughly first.
Self-managed WordPress installations on shared or dedicated servers gave site owners complete control over timing but required them to monitor security announcements and manually initiate updates. The difference meant that a small WordPress blog on a managed hosting platform received automatic protection immediately, while a custom-built site on a virtual private server might have been overlooked if the administrator didn’t actively check for updates. This divergence highlighted the often-overlooked advantage of managed services: they shift security responsibility to specialized teams monitoring threats continuously, even when individual site owners miss announcements.
The Broader Implications for WordPress Security Practices
The emergency patch incident exposed systemic challenges in WordPress security that extend beyond this single vulnerability. WordPress powers such a massive portion of the internet that discovering a critical flaw affecting 12.5 million sites demonstrates the enormous target the platform presents to sophisticated attackers.
The incident accelerated conversations within the WordPress community about the need for more proactive security auditing, faster plugin update distribution mechanisms, and stricter security requirements for plugins before they reach the marketplace. Looking forward, WordPress and the broader ecosystem are likely to implement more aggressive security improvements, potentially including mandatory security scanning for plugin submissions, more frequent core releases addressing security issues, and better communication frameworks for warning site administrators about emerging threats. The massive coordination effort required to patch millions of sites simultaneously highlighted both the strength of the WordPress ecosystem’s response capabilities and the fragility of depending on decentralized update mechanisms across millions of sites with varying capabilities and attention to maintenance.
Conclusion
The WordPress emergency patch addressing the 12.5 million site vulnerability serves as a critical reminder that even mature, well-established platforms remain targets for determined attackers. The speed of the security response—both from the WordPress core team and from hosting providers and the community—demonstrated the strength of the ecosystem’s security practices, yet also exposed gaps in how quickly all sites can receive protection. Site administrators who enabled automatic updates experienced near-instantaneous protection, while those relying on manual processes faced difficult decisions about balancing security risks against stability concerns.
Moving forward, site owners should evaluate their update strategies with security as a priority, ensure automated patching is enabled wherever possible, maintain current backups before applying major updates, and stay informed through multiple notification channels about security threats. The incident also serves as a wake-up call for organizations that depend on WordPress to audit their plugin ecosystems, remove unnecessary extensions, and ensure their hosting environment supports secure, timely patching practices. In an ecosystem of hundreds of millions of sites, distributed security responsibility requires individual administrators to remain vigilant, but centralized coordination from platform providers, hosting companies, and security researchers makes mass protection achievable when threats emerge.