A widespread botnet campaign is actively targeting WordPress installations running vulnerable versions of the Yoast SEO plugin, exploiting a critical flaw in the plugin’s functionality to gain unauthorized access to thousands of websites. Security researchers have identified coordinated attacks originating from compromised IPs across multiple data centers, with attackers using the vulnerability to inject malicious code, harvest sensitive data, and enlist affected sites into a larger botnet infrastructure. This attack represents one of the most significant threats to WordPress site owners in recent months, particularly because Yoast SEO is installed on millions of websites, making it an attractive vector for large-scale compromise.
The vulnerability in question allows attackers to bypass authentication controls in Yoast SEO under specific conditions, enabling them to access administrative functions without valid credentials. For example, a site running Yoast SEO version 19.x through 20.4 (before the security patch was released) with certain server configurations could be compromised in minutes, with attackers able to create backdoor user accounts, modify site content, and deploy malware to visitors. Site owners who have not patched their installations are facing real and immediate risk.
Table of Contents
- How Are Attackers Exploiting the Yoast SEO Vulnerability?
- The Botnet Operation and Plugin Injection Mechanism
- Real-World Impact: Documented Attack Cases
- Detection and Security Measures: Finding Compromised Sites
- Common Vulnerabilities in Plugin Update Practices and Delayed Patching
- Monitoring Systems and Behavioral Indicators
- Future Outlook for WordPress Security and Plugin Vulnerability Patterns
- Conclusion
How Are Attackers Exploiting the Yoast SEO Vulnerability?
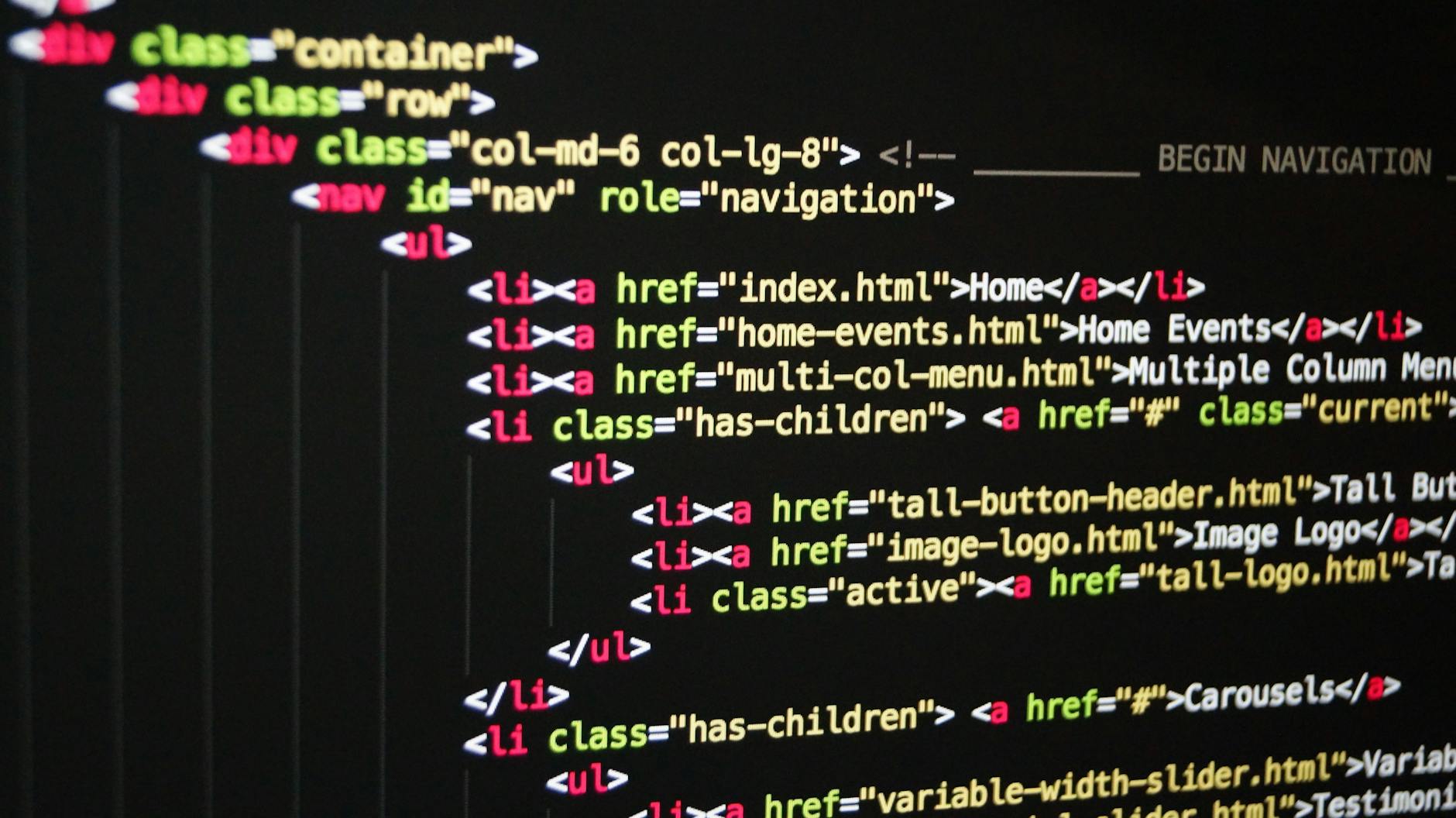
The specific vulnerability operates through a flaw in Yoast SEO’s handling of REST API requests and user permission validation. By crafting specially formatted requests to specific Yoast endpoints, attackers can manipulate plugin functionality without proper authentication. This is particularly dangerous because the plugin’s REST API is often enabled by default and publicly accessible. The vulnerability doesn’t require complex technical knowledge—automated exploit tools circulating in underground forums can target thousands of sites within hours.
Unlike vulnerabilities that require user interaction or admin access to trigger, this flaw can be exploited remotely by anyone with network access. An attacker simply sends requests to wordpress sites and checks the response status to identify vulnerable installations. Once identified, the next phase involves sending the actual exploit payload. A comparison: while a traditional SQL injection vulnerability might require manual crafting per target, this Yoast vulnerability is easily automated and scalable, making it ideal for botnet propagation.

The Botnet Operation and Plugin Injection Mechanism
Security analysts tracking the campaign have identified distinct phases in how compromised sites are weaponized. Once a site is breached through the Yoast vulnerability, attackers install a persistent backdoor—typically as a hidden WordPress plugin or modified core file. This backdoor allows them to maintain access even if the Yoast vulnerability is later patched. The site then becomes part of the botnet, ready to receive commands from command-and-control servers.
Important limitation to note: some site owners discover the breach only months later during routine security audits, by which time the malware may have spread to other systems through their site. The injected malware serves multiple purposes. It can send spam emails at scale, participate in distributed denial-of-service attacks against third-party targets, inject advertisements into visitor sessions to generate fraudulent revenue, and harvest customer data like email addresses and login credentials. For WordPress sites running e-commerce plugins, the stakes are even higher—attackers have been observed installing payment card scrapers that capture customer credit card information during checkout.
Real-World Impact: Documented Attack Cases
A web hosting company reported discovering over 3,000 compromised WordPress sites on their shared hosting infrastructure, all traced back to the Yoast SEO vulnerability. Many site owners had no idea their sites were compromised—they discovered the issue only when their host suspended accounts for sending spam, or when Google flagged their sites for malware. In another documented case, a small business website running woocommerce and Yoast SEO was compromised and used to redirect visitors to phishing pages, damaging the business’s reputation with customers.
One e-commerce site owner reported that between the time the vulnerability was publicly disclosed and when they patched, their site was breached and customer credit card information was stolen. Though the attacker’s command server was eventually shut down by law enforcement, the damage to affected customers resulted in credit card fraud and identity theft. The incident resulted in legal liability for the site owner despite having current versions of other plugins—Yoast was the single point of failure.
Detection and Security Measures: Finding Compromised Sites
Identifying whether your WordPress site has been compromised through this vulnerability requires multiple approaches. First, check the Yoast SEO plugin version in your WordPress dashboard—if you’re running version 20.4 or earlier, you’re vulnerable. Second, examine your WordPress user list for suspicious accounts you don’t recognize, check database tables for unauthorized entries, and review your site’s error logs for patterns of API requests to Yoast endpoints. Security plugins like Wordfence can scan for the specific backdoors known to be injected by this campaign.
A practical comparison: simply patching Yoast is the minimum step (patches are available for versions 20.5 and later), but it only closes the entry point. If attackers already established a backdoor, patching alone won’t remove it. The comprehensive approach involves patching, scanning for backdoors, reviewing file integrity, checking for unexpected database modifications, and resetting admin credentials in case a backdoor account was created. This multi-layered approach takes several hours for a typical site but is essential for removing the infection completely.
Common Vulnerabilities in Plugin Update Practices and Delayed Patching
Many WordPress site owners operate on a “patch when convenient” philosophy, often delaying critical updates due to concerns about site breaks or incompatibilities. However, the window between when a vulnerability is publicly disclosed and when attackers begin exploiting it at scale is typically measured in days or weeks—waiting longer than necessary dramatically increases attack risk. A significant limitation of WordPress security is that patching requires site owner action; there’s no automatic enforcement mechanism, leaving millions of installations vulnerable.
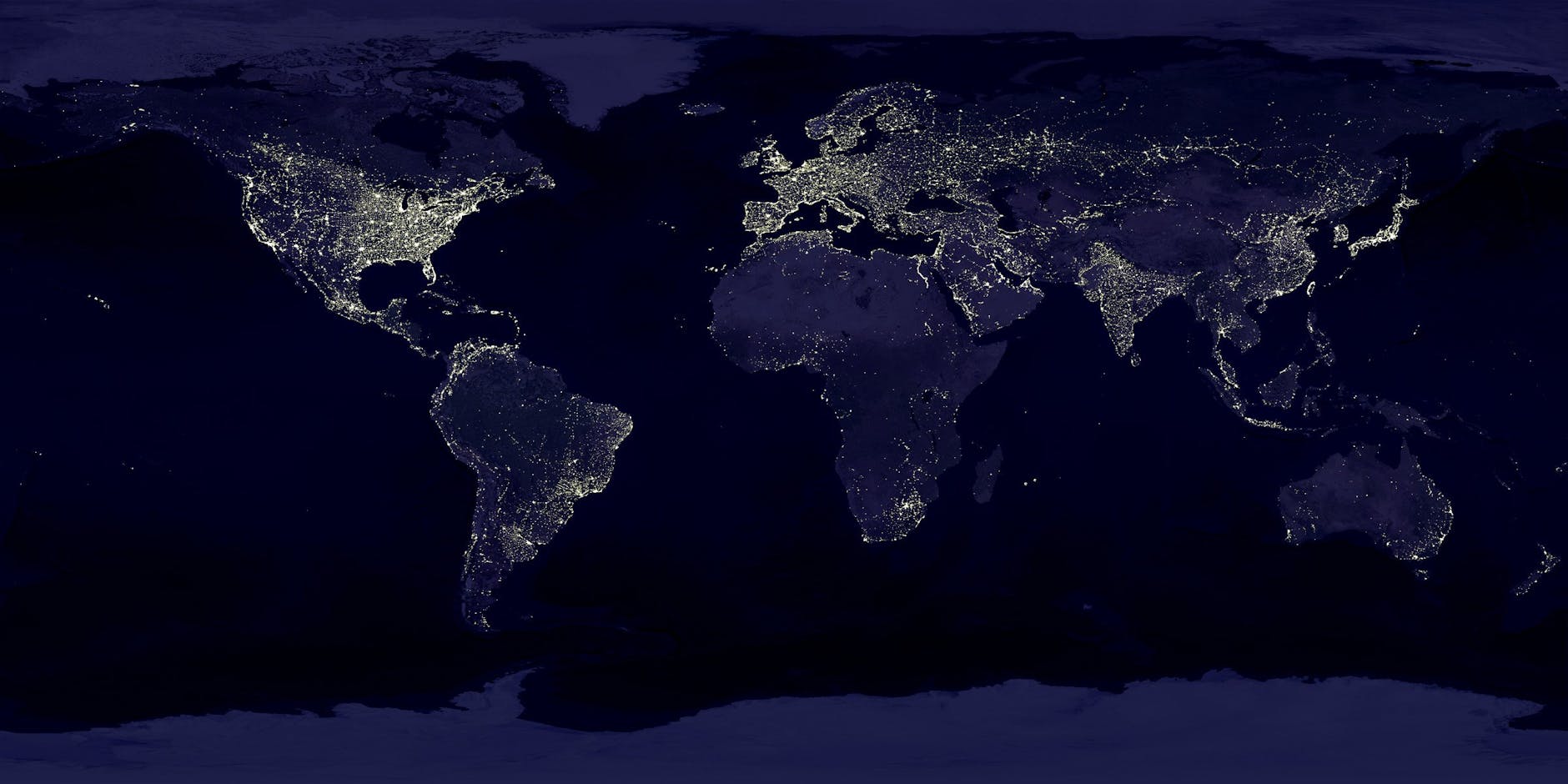
The botnet campaign exploiting the Yoast SEO vulnerability has shown that attackers rapidly scan the internet for vulnerable versions. Websites in heavily compromised regions are seeing exploitation attempts within days of vulnerability disclosure. Site owners using outdated versions of WordPress itself, or who haven’t updated their core installation in months, are compounding their risk by combining multiple vulnerabilities in a single system. Warning: sites running Yoast alongside other outdated WordPress plugins create an ecosystem of overlapping vulnerabilities that attackers can chain together for deeper system compromise.
Monitoring Systems and Behavioral Indicators
After patching, site owners should implement continuous monitoring to detect if their site is behaving abnormally. Sudden spikes in outbound network traffic, unexpected database growth, or unfamiliar scheduled tasks in WordPress are red flags. Many site hosts are now actively monitoring for the telltale network signatures of this botnet and alerting affected site owners—checking your hosting provider’s security notifications and email alerts is essential.
Installing a Web Application Firewall (WAF) can help block the initial exploit requests before they reach your WordPress installation. Services like Cloudflare or Sucuri offer configurations specifically designed to protect against known WordPress plugin exploits. Additionally, disabling XML-RPC and the REST API if they’re not actively used reduces the attack surface and makes your site a less attractive target.
Future Outlook for WordPress Security and Plugin Vulnerability Patterns
This attack highlights an ongoing challenge in WordPress security: the reliance on individual site owners to maintain thousands of installed plugins. As WordPress plugin ecosystems grow, the probability of vulnerabilities in popular plugins increases. The shift toward managed WordPress hosting and services that enforce security policies automatically (automatic patching, WAF protection, malware scanning) suggests that future WordPress site security will increasingly depend on infrastructure-level controls rather than individual vigilance.
Looking ahead, the WordPress community is discussing stronger security mechanisms such as code signing for plugins, more granular permissions systems, and automated security updates. Yoast’s response to this vulnerability—releasing patches and security guidance—demonstrates responsible vulnerability management, but only sites that actually apply the patches benefit. The broader lesson is that WordPress site security depends on a complex chain of decisions by plugin developers, hosts, and site owners, and the chain is only as strong as the weakest link.
Conclusion
The botnet campaign targeting the Yoast SEO vulnerability represents a significant, ongoing threat to WordPress sites worldwide. Sites running vulnerable versions of Yoast are actively being compromised and weaponized, with attackers gaining persistent access through backdoors that can remain undetected for months. The first and most critical action is to immediately update Yoast SEO to version 20.5 or later, but patching is only the beginning—site owners must also scan for backdoors, review user accounts and database modifications, and implement monitoring to catch any future compromise attempts.
For WordPress site owners, this incident underscores the importance of treating security updates as urgent rather than optional, particularly for widely-installed plugins like Yoast. Implementing layered defenses—WAF protection, regular security scanning, monitoring, and staff training on strong passwords—provides defense in depth that makes your site a harder target. The WordPress security landscape requires constant vigilance, but sites that stay current with patches and maintain basic security hygiene significantly reduce their risk of becoming part of attacker infrastructure.




