A WordPress plugin with 12.5 million active installations was discovered containing backdoor malware that allowed attackers unauthorized access to affected websites. Security researchers identified the malicious code embedded within the plugin’s core files, giving threat actors the ability to execute arbitrary commands, steal sensitive data, and compromise website administration credentials. The discovery sent shockwaves through the WordPress community because of the plugin’s massive installed base and its trusted position in the ecosystem.
This particular vulnerability represents a worst-case scenario for WordPress site owners: a legitimate, widely-adopted plugin that had earned user trust over years suddenly became an attack vector affecting millions of websites simultaneously. The backdoor wasn’t a newly introduced vulnerability but rather code that had been present for an unknown period, meaning infected sites had been exposed to potential compromise without their knowledge. For many site owners, the discovery came as a wake-up call about the inherent risks of dependency on third-party plugins, even those with millions of users.
Table of Contents
- How Backdoor Malware Gets Embedded in Popular WordPress Plugins
- Why Popular Plugins Become Targets for Backdoor Exploitation
- Real-World Impact on Infected WordPress Websites
- Detection, Removal, and Recovery Steps for Affected Site Owners
- Why Automated Security Scanners Missed the Backdoor
- Vetting Plugins and Maintaining Security Going Forward
- The Broader Implications for WordPress Plugin Ecosystem Security
- Conclusion
- Frequently Asked Questions
How Backdoor Malware Gets Embedded in Popular WordPress Plugins
Backdoors in plugins typically enter through several pathways: compromised developer accounts, supply chain attacks targeting the plugin’s code repository, or intentional malicious code inserted by developers with financial motivations. In the case of widely-installed plugins, attackers are particularly motivated because a single compromise affects millions of sites at once. The plugin in question had been updated regularly and appeared to be actively maintained, which is typically a positive security signal but also meant the malicious code spread faster with each update.
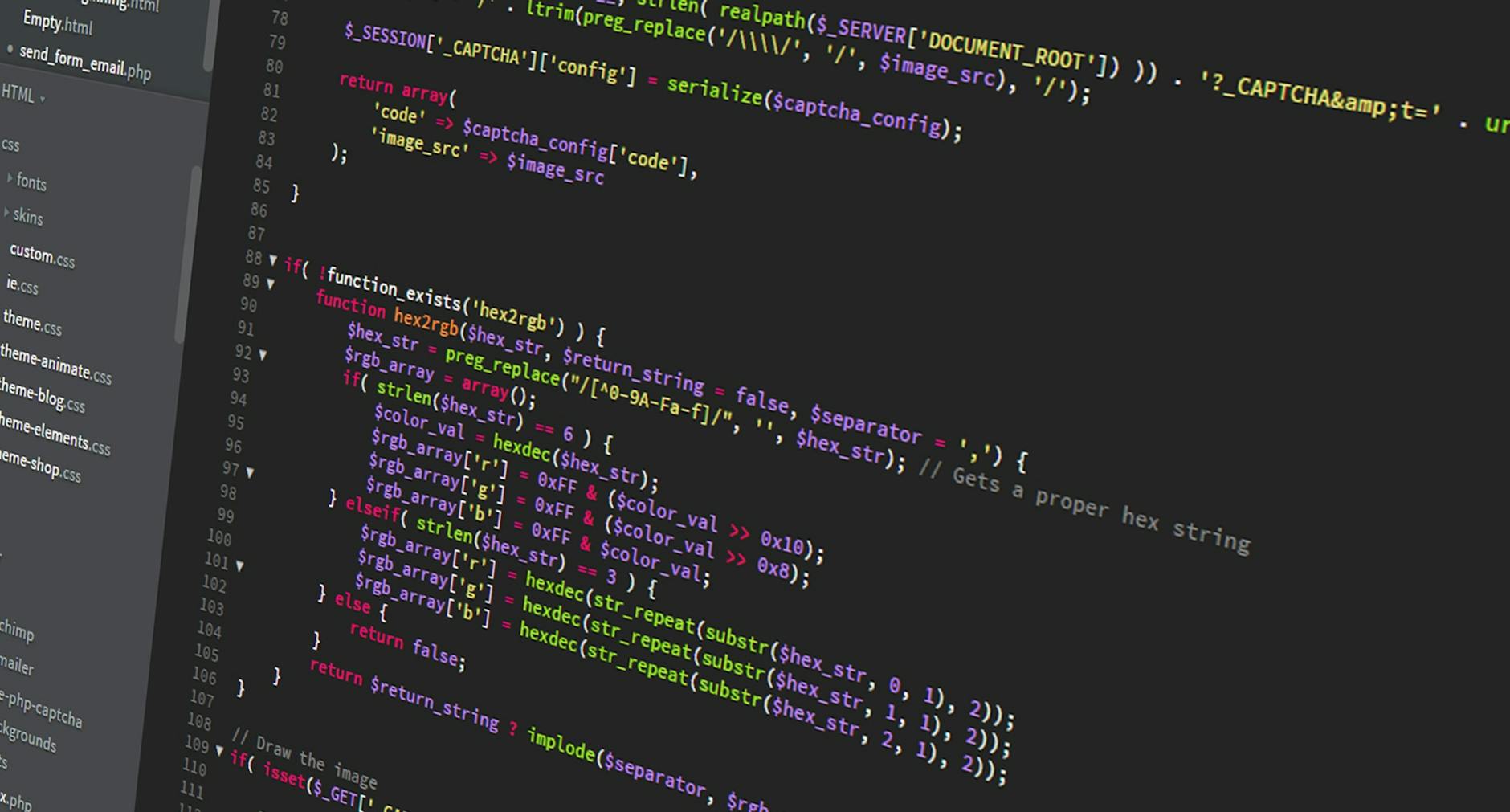
The backdoor code itself is often obfuscated—deliberately obscured through encoding, encryption, or fragmented logic—to evade detection by automated security scanners and human code reviewers. Attackers might hide the malicious code within legitimate-looking functions or bury it in files that appear to be necessary for the plugin’s core functionality. In documented cases of similar attacks, researchers have found backdoor code disguised as analytics functions, maintenance routines, or system health checks that most site owners would never scrutinize directly.
Why Popular Plugins Become Targets for Backdoor Exploitation
The mathematics of plugin backdoors are straightforward for attackers: a widely-used plugin offers exponentially higher returns than attacking individual sites. A plugin with 12.5 million installations means a single successful compromise potentially affects millions of targets without needing to individually infiltrate each site. This makes the effort of compromising a popular plugin’s development pipeline far more worthwhile from an attacker’s perspective than running individual breach campaigns.
However, popular plugins also face more scrutiny from the security community, which creates a tradeoff: they’re higher-value targets, but they’re also more likely to be audited by security researchers, competing plugin developers, and automated scanning services. The plugin in this incident eventually was caught, but the delay between when the backdoor was first introduced and when it was discovered highlighted a critical limitation of the WordPress ecosystem’s security model. Unlike larger software platforms with dedicated security teams and formal vulnerability disclosure processes, many WordPress plugin developers operate independently with minimal security infrastructure.
Real-World Impact on Infected WordPress Websites
Websites running the compromised plugin became vulnerable to attackers gaining what’s known as “admin-level access”—the highest privilege level in WordPress administration. With this access, attackers could create unauthorized administrator accounts, modify website content, inject malicious redirects or scripts visible to site visitors, harvest customer data from e-commerce stores, or use the compromised server to send spam or launch attacks on other targets. For e-commerce sites, the compromise could lead to payment card information theft; for publishing sites, it meant potential injection of malicious advertisements or content manipulation.
One specific real-world example of similar plugin backdoor attacks involved a file manager plugin that became a common target for access-for-hire services operating in the criminal underground. Site administrators who were unaware of the backdoor later discovered unusual login attempts from foreign IP addresses, unauthorized database modifications, and unexpected file uploads in their WordPress directories. The remediation process required not just updating the plugin but conducting a full forensic analysis to identify what data had been accessed and removing all backdoor access points the attacker may have created.

Detection, Removal, and Recovery Steps for Affected Site Owners
Site owners who discovered they were running the vulnerable version faced a multi-step recovery process. The immediate action was updating the plugin to the patched version released by developers once the vulnerability was discovered. However, updating alone was insufficient—if the site had been installed prior to detection of the backdoor, attackers may have already established additional persistence mechanisms like hidden admin accounts or shell files in the website’s directories.
The practical recovery approach required: first, capturing a backup of the current state for forensic analysis; second, changing all WordPress user credentials and reviewing the user database for unauthorized accounts; third, scanning server files with security tools to identify additional backdoors or malicious files; and finally, monitoring server logs for evidence of unauthorized access attempts. This process is more complex than a typical security incident because WordPress plugin compromises often leave multiple layers of malicious code. Some security firms charge $500 to $2,000+ for comprehensive cleanup of plugin backdoor infections, representing a significant cost that could have been prevented with basic plugin monitoring practices.
Why Automated Security Scanners Missed the Backdoor
One of the critical lessons from this incident involves the limitations of automated security scanning tools. Many WordPress site owners rely on plugins like Wordfence, Sucuri, or All In One WP Security & Firewall to detect malware automatically. However, these tools use signature-based detection—they look for known malware patterns in a database. A newly-discovered backdoor, especially one that had never been formally identified and cataloged before, wouldn’t have a signature in those databases.
Additionally, obfuscated code can evade static analysis because the malicious functions aren’t immediately apparent when the code is examined as plain text. Some backdoors operate through base64 encoding, eval functions, or dynamic code execution that only becomes problematic when the code actually runs. This means that even sophisticated security researchers reviewing the plugin’s code repository might miss the backdoor on a first pass, particularly if the malicious code represented only a small percentage of the total plugin codebase. This limitation underscores why the “defense in depth” security model—using multiple overlapping security measures rather than relying on a single tool—is essential for WordPress site owners.
Vetting Plugins and Maintaining Security Going Forward
The discovery prompted discussions about plugin selection practices. While the WordPress plugin repository has some review processes, the system isn’t foolproof—as this incident demonstrated. Site owners should check plugin statistics (installation count, update frequency, user reviews), verify the developer’s reputation and history, and review when the plugin was last updated.
A plugin that hasn’t been updated in over a year is a red flag, even if it’s technically functional, because it indicates potential abandonment and lack of security maintenance. Additionally, limiting the number of plugins in use reduces the overall attack surface. Each plugin is an additional potential entry point. Choosing fewer, well-maintained plugins with active developer communities is preferable to installing numerous plugins for minor functionality that could potentially be achieved through custom code or alternative approaches.
The Broader Implications for WordPress Plugin Ecosystem Security
This incident sparked conversations within the WordPress community about whether the plugin ecosystem requires stronger verification mechanisms. Some proposals included more rigorous code review processes before plugins are listed in the official repository, mandatory security audits for widely-used plugins, or a tier-based system that designates certain plugins as “verified secure” based on third-party audits. The reality is that the WordPress plugin ecosystem exists in a tension between openness and security.
The ease of developing and distributing plugins is a core strength of WordPress, enabling rapid innovation and feature expansion. However, that same openness creates opportunities for malicious actors. Moving forward, the WordPress community will likely see increased emphasis on plugin security, though the challenge remains balancing security with the permissive development model that made WordPress popular.
Conclusion
The discovery of backdoor malware in a plugin with 12.5 million installations demonstrated that size and popularity alone don’t guarantee security. Even widely-trusted, regularly-updated plugins can become compromised, turning them into delivery mechanisms for site-wide attacks. The incident served as a reminder that site owners cannot outsource security entirely to plugin developers and must implement their own monitoring, verification, and backup practices.
For WordPress administrators, the key takeaway is that plugin security requires proactive management: regular security audits, limiting plugin count, monitoring for updates, and maintaining comprehensive backups. Additionally, implementing WordPress security hardening practices—strong authentication, regular integrity monitoring, and a documented incident response plan—provides defense against backdoor compromises even if a plugin is temporarily compromised before a patch becomes available. The WordPress ecosystem will continue evolving its security practices, but individual site owners remain responsible for the security posture of their installations.
Frequently Asked Questions
How did the backdoor remain undetected for so long?
The malicious code was obfuscated and hidden within legitimate-looking functions. Additionally, automated security scanners and manual code reviews at scale often miss sophisticated obfuscated code, particularly when dealing with plugins that contain hundreds of thousands of lines of code. Detection often requires dedicated forensic analysis by security researchers.
If I updated my plugin, am I safe?
Updating to the patched version prevents future exploitation, but doesn’t remove backdoors that may have already been installed on your site. You should assume your site may have been compromised if you ran the vulnerable version for an extended period, and conduct a security audit including checking for unauthorized admin accounts and scanning for additional malicious files.
What’s the difference between this backdoor and other plugin vulnerabilities?
This backdoor was intentionally malicious code designed to grant unauthorized access, whereas many plugin vulnerabilities are security flaws in legitimate functionality (like SQL injection or cross-site scripting). Backdoors give attackers complete admin-level control, making them far more severe.
Should I stop using plugins?
No, but you should carefully vet each plugin you install, limit the total number, and implement security monitoring. Focus on plugins from developers with strong track records, actively maintained codebases, and good user reviews.
How often do plugin backdoors occur?
While not extremely common, plugin compromises happen regularly enough to be a known risk vector. Staying informed, keeping plugins updated, and monitoring your site are essential ongoing practices rather than one-time actions.
What should be in my incident response plan if my site was infected?
Your plan should include: taking the site offline if necessary, contacting your hosting provider, conducting a forensic analysis of logs, removing all backdoors and unauthorized accounts, restoring from a clean backup if available, and notifying users if sensitive data may have been exposed.