Securing a Drupal site before launch requires patching critical vulnerabilities, disabling verbose error reporting, enforcing HTTPS, implementing two-factor authentication for administrators, and running the official Drupal Security Audit Checklist. This isn’t optional maintenance—it’s the foundation that keeps your site operational and prevents attackers from exploiting common entry points on day one. The stakes are high: unsecured Drupal instances become targets within hours of going live, and a single unpatched vulnerability can lead to remote code execution, data theft, or complete site compromise.
The urgency is real. In April 2026 alone, Drupal released three core security advisories, including a critical XSS vulnerability affecting jQuery AJAX modal dialog boxes and a moderately critical deserialization flaw that could enable SQL injection or remote code execution. If your launch date is within weeks of a security release, you cannot assume patches are optional—they are prerequisites. A robust pre-launch security process takes 2-4 weeks depending on your site’s complexity, but it eliminates the majority of common attack vectors before they become incidents.
Table of Contents
- What Drupal Core Patches Must You Install Before Launch?
- How Do You Harden Drupal Configuration Settings for Production?
- Why Is Two-Factor Authentication for Admins Critical Before Launch?
- How Do HTTPS and SSL Certificates Protect Your Drupal Site?
- Which Contributed Modules Create Pre-Launch Security Risks?
- What Does a Pre-Launch Security Checklist Actually Include?
- How Should You Test Security Before Going Live?
- Conclusion
- Frequently Asked Questions
What Drupal Core Patches Must You Install Before Launch?
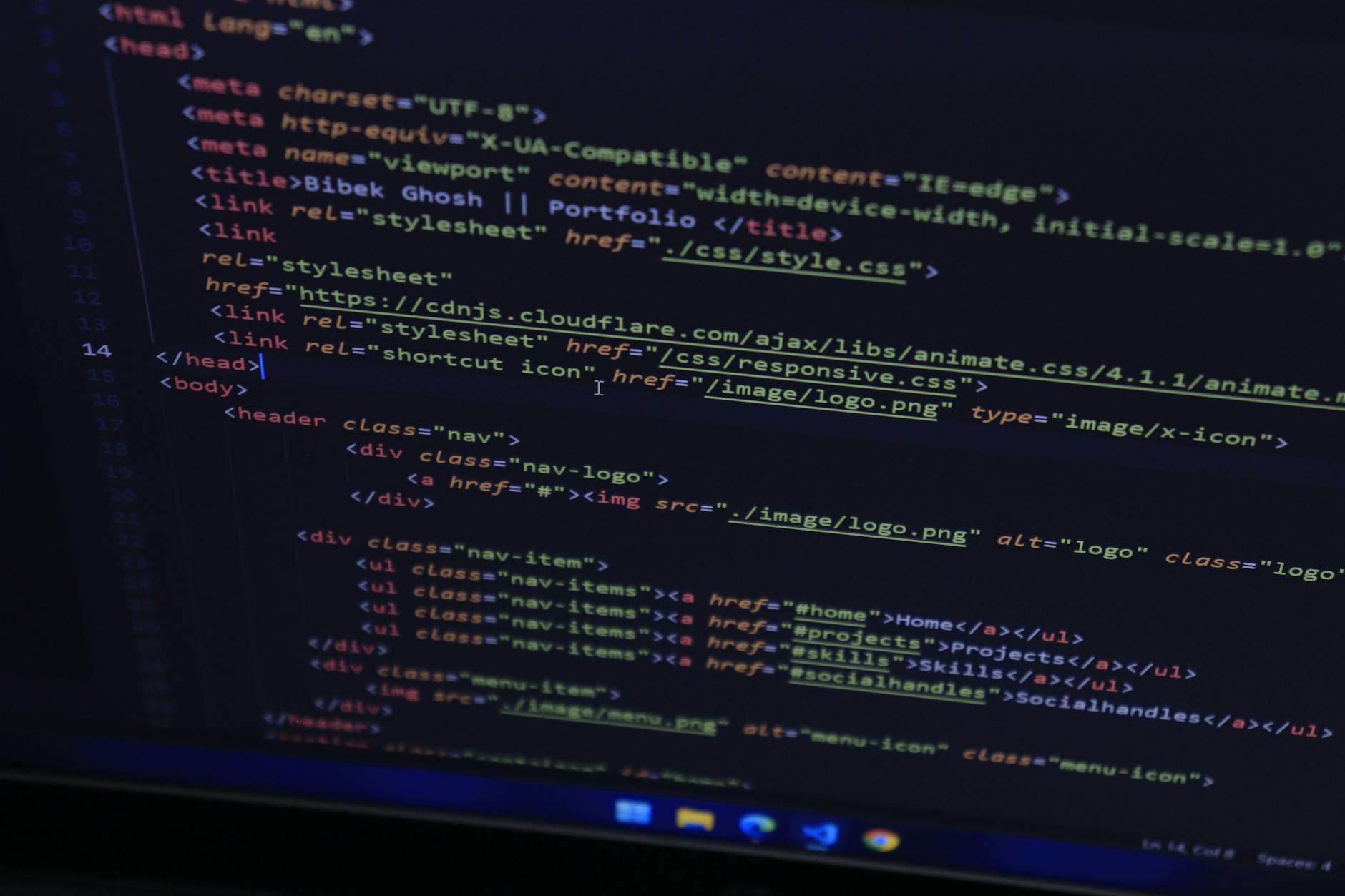
You must update to Drupal 10.5.9, 10.6.7, 11.2.11, or 11.3.7 or later before your site goes live. These versions address the April 2026 vulnerability announcements: SA-CORE-2026-001 (critical XSS in jQuery AJAX modals), SA-CORE-2026-002 (deserialization gadget chain leading to RCE), and SA-CORE-2026-003 (stored XSS via CKEditor 5 entity suggestions). Delaying this update because your site is “almost ready” is the most common pre-launch mistake—attackers scan for unpatched Drupal instances within 24 hours of launch, and they will find you.
If you’re running Drupal 10, you have until December 2026 of official support, which gives you a runway for gradual upgrades. However, each minor version within Drupal 10 and 11 may receive security patches on different timelines. Subscribe to the Drupal security advisory mailing list and check drupal.org/security regularly during your final weeks before launch. A single missed patch is enough to create a critical incident on day one.
How Do You Harden Drupal Configuration Settings for Production?
Start by turning off on-screen error reporting at Configuration > Development > Logging and errors. Production sites should log errors to disk or a remote logging service, not display stack traces to visitors. This prevents information disclosure: error messages reveal your Drupal version, installed modules, file paths, and database structure—all reconnaissance data attackers use to plan attacks. Set your site to “Production” mode, not “Development,” and verify that the error reporting option is set to log-only, not log and display.
Beyond error reporting, you’ll want to implement Content Security Policy (CSP) headers, set appropriate cache headers to prevent sensitive data from being stored by intermediaries, and disable PHP file execution in upload directories. Many teams skip these configuration steps because they don’t cause obvious problems during testing. But they create exploitable weaknesses: for example, if an attacker uploads a malicious PHP file to a media directory and PHP can execute it, they gain immediate code execution. These hardening steps take 1-2 days but eliminate entire classes of attacks.
Why Is Two-Factor Authentication for Admins Critical Before Launch?
Administrative accounts are the single most valuable target for attackers. A compromised admin account gives attackers the ability to modify content, install malicious modules, create backdoor accounts, and exfiltrate data without any additional effort. Two-factor authentication (2FA) on all administrator accounts raises the barrier dramatically—an attacker needs not only a password but also a second factor (typically a time-based code from an authenticator app) to gain access.
Implement 2FA using Drupal’s TOTP (Time-based One-Time Password) module or an equivalent authentication module before launch. Train your admin team on the process during your pre-launch testing period so they’re not fumbling with 2FA on day one. It adds 5-10 seconds to each login but prevents the most direct path to site compromise. Consider also restricting admin account login to known IP addresses if your team works from a fixed office or uses a VPN.
How Do HTTPS and SSL Certificates Protect Your Drupal Site?
HTTPS encrypts the connection between visitor browsers and your server, preventing attackers on the same network (or between your visitor and your server) from eavesdropping on passwords, session tokens, or user data. If your site collects any user input—comments, contact forms, user accounts—you must have a valid SSL certificate and redirect all traffic to HTTPS before launch. Modern browsers flag HTTP sites as “not secure,” which degrades user trust and harms SEO.
Install your SSL certificate and configure your web server (Apache or Nginx) to redirect all HTTP traffic to HTTPS at the configuration level, not within Drupal. Verify the redirect works and that your site loads correctly over HTTPS, including all images, stylesheets, and scripts—mixed content (some resources over HTTP, others over HTTPS) will break modern browsers and look suspicious to visitors. Let’s Encrypt offers free SSL certificates if budget is tight, but you can also use certificates from commercial providers. Test your certificate installation at ssl-labs.com to confirm it meets current security standards.
Which Contributed Modules Create Pre-Launch Security Risks?
Contributed modules (third-party extensions) are often the source of exploitable vulnerabilities. In April 2026, eight CVEs were disclosed in Drupal 7 contrib modules alone, and similar issues appear regularly across Drupal versions. Before launch, audit every contributed module you’ve installed: visit drupal.org/security and search for known vulnerabilities in each module by name. Disable and remove any modules with unpatched critical or moderately critical vulnerabilities.
The temptation is strong to launch with a “nice to have” module and patch it later. Resist that impulse. A single unpatched contrib module is just as dangerous as an unpatched core vulnerability, sometimes more so because contrib modules get less visibility and slower updates. During your final pre-launch security review, run a Drupal security audit tool (such as the Security Audit Checklist module) to identify problematic contrib modules automatically. If a module has a critical vulnerability with no patch in sight, either remove it or replace it with a maintained alternative before launch.
What Does a Pre-Launch Security Checklist Actually Include?
Drupal.org provides official launch checklists via the Launch Checklist module (14 sections) and the Security Audit Checklist module. These aren’t theoretical—they’re based on incidents and common mistakes from thousands of Drupal launches. The Launch Checklist covers database backups, file permissions, performance tuning, and analytics setup.
The Security Audit Checklist focuses specifically on security configurations: it checks whether error reporting is disabled, whether file permissions are restrictive, whether common backdoor patterns exist, and whether sensitive files are protected from web access. Run both checklists 2-3 weeks before your launch date and address every “fail” item before launch day. Some items are quick fixes (a permission change); others require more planning (switching authentication methods). A mature pre-launch process builds in time to address these findings without rushing.
How Should You Test Security Before Going Live?
Testing security before launch is different from testing functionality. You’re not checking whether your contact form sends emails; you’re checking whether someone can submit malicious code through that form and compromise the server. Conduct at least a basic manual security test: attempt SQL injection in search fields, try uploading malicious files, attempt to bypass user permissions, and verify that admin pages require authentication.
Consider hiring a professional penetration tester if your site handles payment information, user accounts, or sensitive data. The cost ($2,000-$10,000 for a focused pre-launch test) is insurance against the much larger cost of a post-launch compromise. If budget is tight, run the Drupal security checklist module, ensure all patches are applied, and have a team member (who isn’t the main developer) manually test the site with security in mind. Many security issues are discovered not by sophisticated attackers but by someone simply trying to break the site the wrong way.
Conclusion
Securing a Drupal site before launch is not a optional checklist item—it’s the primary prerequisite for a stable, trustworthy site. Start with patching Drupal core to the latest secure version (10.5.9, 10.6.7, 11.2.11, or 11.3.7+), hardening configuration settings by disabling error reporting and enabling HTTPS, implementing two-factor authentication for administrators, and auditing contributed modules for known vulnerabilities. Then run the official Drupal.org security checklists and conduct at least basic security testing before launch day.
The window between your final pre-launch review and going live is narrow, so plan your security work 4-6 weeks ahead of launch. Every day you delay on security patches or hardening increases the risk that a vulnerability will be exploited within hours of launch. Build security into your launch timeline as a non-negotiable phase, not an afterthought, and you’ll avoid the costly incident that derails your first weeks in production.
Frequently Asked Questions
Can I patch Drupal after launch if I’m running out of time?
No. Unpatched vulnerabilities are discovered by automated scanners within hours of launch. If launch day is approaching and you haven’t patched, delay launch. A week of delay is far cheaper than incident response, reputational damage, and data recovery after a compromise.
Does the Drupal Security Audit Checklist module slow down my site?
No, it’s a administrative tool that runs only when you visit the audit page. It doesn’t affect site performance.
How often should I update Drupal after launch?
Critical and moderately critical security patches should be applied within days of release. Regular minor/patch updates should be scheduled at least monthly. Subscribe to the Drupal security mailing list to stay informed.
What’s the difference between core and contrib module vulnerabilities?
Core vulnerabilities affect the Drupal foundation and are patched quickly and universally. Contrib vulnerabilities depend on individual module maintainers and may never be patched. This is why contrib modules with vulnerabilities should be disabled or removed before launch.
Does HTTPS alone protect against hacking?
HTTPS encrypts data in transit, preventing eavesdropping. It doesn’t protect against attacks on the application itself (like SQL injection or XSS). HTTPS is necessary but not sufficient—you need both encrypted communication and secure application configuration.
How long should pre-launch security testing take?
Basic testing (running security audit modules and manual testing) takes 1-2 weeks. A professional penetration test adds 2-4 weeks. Plan accordingly in your launch timeline.




