PHP sessions are the backbone of user authentication in web applications, maintaining login state across multiple page requests without requiring users to enter their credentials repeatedly. A PHP session creates a unique identifier (session ID) for each user and stores associated data on the server side, allowing you to track whether a user is logged in, store their preferences, and manage their access to protected areas of your application. For example, when a user logs into a WordPress dashboard, PHP creates a session containing their user ID and role information, enabling WordPress to verify their identity on every subsequent request without querying the database for their password.
Sessions work by storing a session ID in a cookie on the user’s browser, while the actual session data remains on your server. This separation of concerns—storing sensitive information on the server while only transmitting an identifier to the client—is what makes sessions fundamentally more secure than storing user data directly in cookies. When the user’s browser makes a request, the session ID is sent along with it, and your PHP application uses that ID to retrieve the corresponding session data from storage, allowing your code to access user information through the `$_SESSION` superglobal.
Table of Contents
- What Are PHP Sessions and How Do They Maintain User Login State?
- Session Security Best Practices and Configuration
- Session ID Regeneration and Preventing Session Fixation Attacks
- Implementing Session Timeout and Idle Management
- Handling Session Data and Storage Considerations
- PHP Version Support and Session Security Updates
- Session Management in Modern Web Development
- Conclusion
What Are PHP Sessions and How Do They Maintain User Login State?
php sessions work through a process of initialization and retrieval that happens automatically when you call `session_start()` at the beginning of your script. This function checks whether a session ID exists in the incoming request (typically in a cookie called PHPSESSID), and if so, retrieves the session data from storage on your server. If no session ID exists, PHP generates a new one and creates a new session. All subsequent references to `$_SESSION` throughout your script are automatically persisted to the server-side storage when the script completes execution.
The session ID itself is a critical security component, and PHP’s default session ID generation already provides sufficient entropy for most applications. However, the industry standard requires session identifiers to have at least 64 bits of entropy to prevent attackers from guessing valid session IDs through brute-force attacks. If you implement custom session ID generation, you must use cryptographically secure pseudorandom number generators with at least 128 bits of entropy to maintain an adequate security margin. PHP’s built-in `session_create_id()` function generates IDs with sufficient entropy by default, making it the safest choice for custom implementations when you need to override PHP’s default behavior.

Session Security Best Practices and Configuration
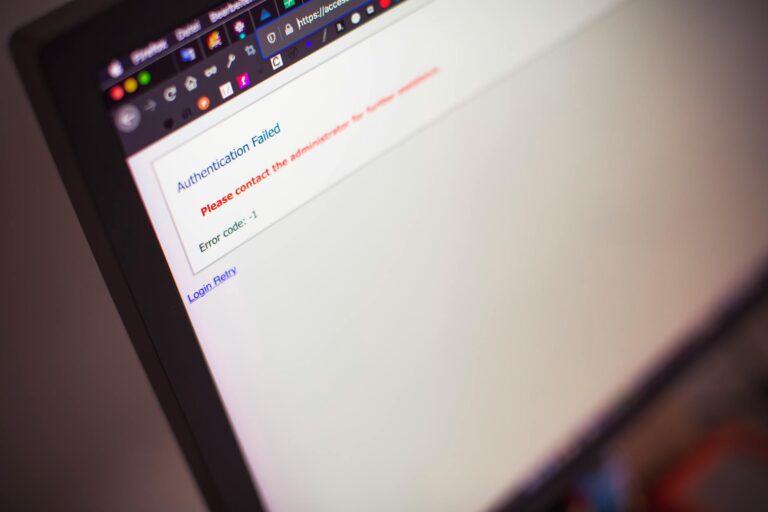
The most critical security consideration for sessions is preventing unauthorized access to session data, which requires configuring three essential cookie security flags in your PHP configuration. The Secure flag ensures that session cookies are only transmitted over HTTPS connections, preventing interception over unencrypted HTTP. The HttpOnly flag prevents JavaScript code from accessing the session cookie, which stops cross-site scripting (XSS) attacks from stealing session IDs.
The SameSite attribute, set to ‘Strict’, provides defense against cross-site request forgery (CSRF) attacks by ensuring cookies are only sent in requests originating from your own domain. You can enable these flags by configuring your `php.ini` file with `session.cookie_secure = 1`, `session.cookie_httponly = 1`, and `session.cookie_samesite = Strict`. A critical limitation of the Secure flag is that it requires HTTPS on your entire site—if your application serves any pages over HTTP, session cookies won’t be transmitted, and users will appear logged out. This is actually a desirable limitation from a security perspective, as it forces you to implement HTTPS throughout your application, but it does create a migration challenge for legacy applications transitioning from HTTP to HTTPS.
Session ID Regeneration and Preventing Session Fixation Attacks
Session fixation is an attack where an attacker tricks a user into using a known session ID, potentially allowing the attacker to predict or control the session ID before the user logs in. PHP provides the `session_regenerate_id()` function to defend against this attack by creating a new session ID while preserving the existing session data. The critical implementation detail is calling `session_regenerate_id(true)` with the true parameter, which deletes the old session file immediately, preventing attackers from using both the old and new session IDs simultaneously.
You must call `session_regenerate_id(true)` at critical security transitions, including immediately after a user successfully logs in, before setting any authentication-related data to `$_SESSION`. The same regeneration should occur when a user’s privilege level changes (such as promoting them to administrator) or when they access a sensitive operation. For example, a WordPress plugin handling sensitive operations should regenerate the session after confirming the user’s credentials, ensuring that any attacker who was previously using a brute-forced session ID cannot maintain access to the elevated privilege level. Additionally, enable `session.use_strict_mode = 1` in your PHP configuration, which causes PHP to reject uninitialized session IDs and create a new one instead, further preventing attackers from forcing users to use known session IDs.
Implementing Session Timeout and Idle Management
User idle timeouts are a practical security mechanism that automatically logs out inactive users, limiting the window of opportunity for session hijacking. The OWASP security guidelines recommend different timeout periods depending on your application’s risk profile: highly protected applications handling sensitive data should implement 5-minute idle timeouts, while lower-risk applications can allow timeouts up to 30 minutes. This creates a tradeoff between security and user experience—shorter timeouts provide better security but require users to log in more frequently, while longer timeouts offer convenience at the expense of security. Implementing idle timeouts requires custom code since PHP doesn’t provide built-in idle timeout functionality; you must track the last activity timestamp in the session and check it on each request.
A straightforward implementation stores `$_SESSION[‘last_activity’]` with the current timestamp, then compares the current time to this stored value. If the idle period exceeds your threshold, you destroy the session with `session_destroy()` and redirect the user to the login page. The comparison in the example below demonstrates a 20-minute timeout: `if (isset($_SESSION[‘last_activity’]) && (time() – $_SESSION[‘last_activity’] > 1200)) { session_destroy(); }`. This same timeout value should also have a maximum absolute session lifetime—typically 8 to 12 hours—to prevent sessions from remaining valid indefinitely even if the user maintains activity.
Handling Session Data and Storage Considerations
By default, PHP stores session data in temporary files on the server’s filesystem, which works adequately for small to medium applications but creates performance and scalability challenges. The default file-based storage saves each session as a separate file in the directory specified by `session.save_path`, with the filename being the session ID. This approach has a critical limitation: distributed applications running on multiple servers cannot access each other’s session files, so users might be logged in on one server but appear logged out on another. For applications requiring high availability or running on multiple servers, you should configure session storage to use a distributed backend like Redis, Memcached, or a database.
The storage choice involves tradeoffs between performance, persistence, and complexity. Redis offers excellent performance with automatic session expiration support, while database storage provides better integration with your existing infrastructure but requires more queries. If your application is running on a single server or within a containerized environment where your servers share a common storage backend, the default filesystem storage remains appropriate. However, WordPress and other popular PHP applications recommend Redis as the preferred session storage backend for production deployments.

PHP Version Support and Session Security Updates
As of 2026, PHP 8.1 and PHP 8.2 reached end-of-security-support on December 31, 2025, meaning they no longer receive security patches. PHP 8.3 continues to receive security updates through mid-2026, while PHP 8.4 is the current recommended production version for new deployments. This matters for sessions because older PHP versions may have unpatched session-related security vulnerabilities that attackers could exploit.
Applications running on unsupported PHP versions should prioritize upgrading, as session security is only as strong as the PHP interpreter itself. Each PHP version brings incremental improvements to session security through better default configurations and additional security functions. For instance, PHP 7.1 introduced the SameSite cookie attribute and improved session ID generation algorithms. When upgrading your PHP version, always review the session-related changes in the release notes and test your session implementation thoroughly, as some hosting providers may have changed default session configurations during the upgrade process.
Session Management in Modern Web Development
Modern web development frameworks like Laravel, Symfony, and WordPress typically provide abstraction layers over PHP’s native session functions, offering more secure defaults and additional features like session middleware and automatic CSRF protection. However, understanding the underlying PHP session mechanism remains essential because these frameworks are built on top of PHP’s session handling, and misconfiguration at the PHP level can compromise even well-designed framework implementations.
Many WordPress plugins and themes directly interact with `$_SESSION`, making it important to understand how sessions work when developing for the WordPress ecosystem. The shift toward stateless authentication in API-based architectures has led some developers to assume sessions are becoming obsolete, but traditional session-based authentication remains the standard for server-rendered web applications and continues to be the default approach in WordPress, Drupal, and other PHP-based content management systems. While newer token-based approaches (JWT, OAuth) are valuable for certain use cases, sessions offer built-in CSRF protection, easier implementation, and better user experience for server-rendered applications, ensuring they’ll remain a core component of PHP development for years to come.
Conclusion
PHP sessions are a mature, well-established mechanism for managing logged-in users that remains foundational to web development. Implementing sessions securely requires attention to multiple details: configuring cookie security flags (Secure, HttpOnly, SameSite), regenerating session IDs at critical transitions, implementing idle timeouts, and ensuring your PHP version is supported with current security patches. These practices are not optional extras but fundamental requirements that directly impact your application’s ability to prevent unauthorized access, session hijacking, and session fixation attacks.
Your implementation should begin with enabling strict session security settings in `php.ini`, calling `session_regenerate_id(true)` immediately after successful login, and implementing custom idle timeout logic to automatically log out inactive users. For production applications, consider storing sessions in Redis or a database rather than relying on filesystem storage, particularly if you operate multiple servers. By understanding how sessions work and implementing these security practices, you create a solid foundation for user authentication that will protect both your application and your users’ accounts.