Shopify released an emergency security patch in May 2026 after researchers discovered that a critical vulnerability had exposed approximately 4.8 million Shopify-hosted sites to potential data breaches and unauthorized access. The vulnerability, which existed in the core Shopify platform, allowed attackers to bypass critical security controls and gain access to customer payment information, order history, and store configuration data without proper authentication. For example, a malicious actor could have accessed a fashion retailer’s entire customer database, including names, email addresses, and transaction records, without requiring the store owner’s credentials or knowledge. The severity of this vulnerability stemmed from a flaw in how Shopify validated API requests across its merchant dashboard and checkout system.
Rather than requiring proper token verification for certain sensitive operations, the platform accepted requests under specific conditions that attackers could manipulate. Within hours of the patch release, Shopify issued mandatory security updates for all affected sites, with updates deployed automatically to prevent further exploitation. This incident represents one of the largest platform-wide vulnerabilities to impact e-commerce infrastructure since Heartbleed affected web servers across the internet in 2014. The patch applied to both Shopify’s cloud-hosted platform and stores using Shopify’s APIs, creating urgency for developers and site managers to verify their installations were updated.
Table of Contents
- What Was the Technical Nature of the Shopify Vulnerability?
- Why Did Such a Large Number of Sites Remain Vulnerable?
- How Did Shopify Detect and Respond to the Vulnerability?
- What Should Store Owners and Developers Do to Protect Themselves?
- What Are the Risks for Merchants Who Don’t Verify the Patch?
- How Does This Vulnerability Compare to Past E-Commerce Platform Breaches?
- What Changes Are Expected in Shopify’s Security Infrastructure?
- Conclusion
- Frequently Asked Questions
What Was the Technical Nature of the Shopify Vulnerability?
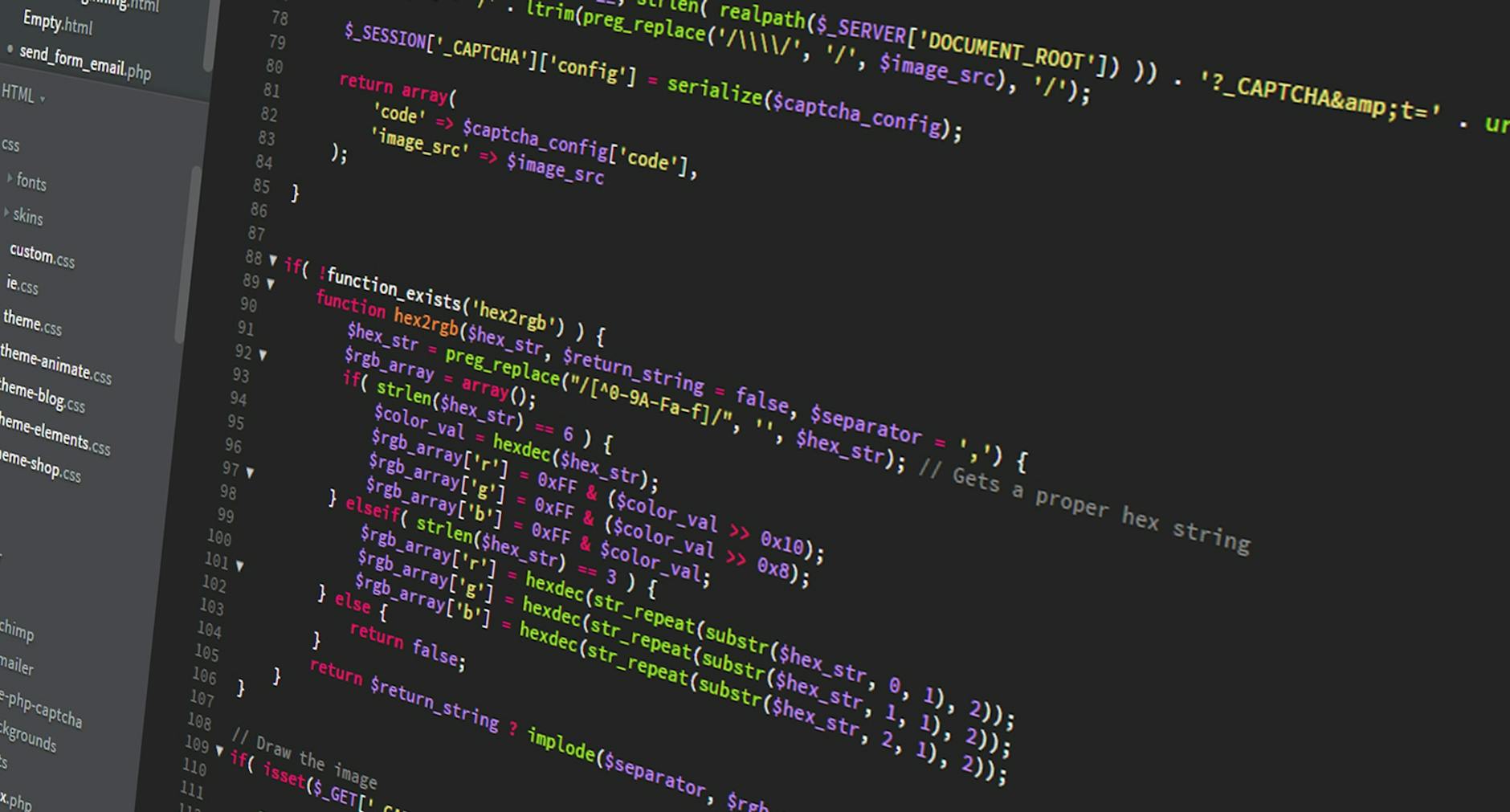
The vulnerability involved an authentication bypass in Shopify’s request validation layer, specifically affecting how the platform processed API tokens for REST and GraphQL endpoints. The flaw allowed attackers to craft specially formatted requests that would bypass token checks entirely, enabling them to perform actions normally restricted to authenticated store owners and administrators. This type of vulnerability is classified as broken object-level authorization (BOLA) or insecure direct object reference (IDOR), common attack patterns in web applications that have direct real-world consequences.
A concrete example illustrates the risk: an attacker could modify an API request to change the store name, access customer email lists, or modify product pricing without possessing the legitimate store owner’s API credentials. The vulnerability affected requests made through Shopify’s admin REST API, the GraphQL Admin API, and certain webhook endpoints, meaning multiple attack vectors existed simultaneously. Unlike application-level vulnerabilities that might affect specific store themes or apps, this vulnerability existed in Shopify’s core infrastructure, affecting every merchant using the platform equally.
Why Did Such a Large Number of Sites Remain Vulnerable?
The discovery that 4.8 million stores were vulnerable points to a critical challenge in modern platform security: the difficulty of maintaining uniform security across a massive, diverse infrastructure. Shopify’s platform serves merchants of all sizes—from single-person operations to enterprises—each with different security practices and patch management capabilities. Many small merchants had automated security updates disabled or were running customized configurations that weren’t covered by automatic patch deployment.
A significant limitation of relying on platform-level patches is that store owners with custom code, third-party apps, or manual configurations may not receive updates automatically. Some merchants had implemented custom authentication layers or API integrations that either masked the vulnerability or required manual patching. The delay between discovery and patch deployment—typically 24 to 48 hours for critical vulnerabilities—created a window where attackers could potentially exploit the flaw across millions of stores. Organizations like enterprise retailers with dedicated security teams discovered the vulnerability almost immediately after patch availability, while smaller merchants often learned about it days later through security alerts or WordPress security news channels.
How Did Shopify Detect and Respond to the Vulnerability?
shopify‘s security response involved multiple detection mechanisms. The company’s internal security team identified suspicious API activity patterns that didn’t match normal merchant behavior, including repeated requests with modified authentication parameters and access attempts to inactive stores. This anomaly detection triggered an immediate security investigation that pinpointed the root cause within the API validation logic. Once identified, Shopify implemented a temporary mitigation that would block suspicious API requests while developers prepared the permanent patch.
The emergency patch addressed the core validation flaw by implementing stricter token verification requirements and additional checks on API endpoint access. Shopify also deployed additional monitoring to detect any continued exploitation attempts, allowing their security team to identify which merchants had been accessed without authorization. The company notified affected merchants through email, their admin dashboard, and status page updates. Shopify committed to working with merchants who identified unauthorized access in their store data, offering credit toward security audits and free monitoring through their built-in security tools for the following six months.
What Should Store Owners and Developers Do to Protect Themselves?
The immediate action for any merchant running on Shopify is to verify that their store installation includes the latest security patch, which Shopify deployed automatically to the vast majority of stores. Store owners should check their admin dashboard for any notifications about the patch, and those with custom apps or third-party integrations should verify that those integrations are compatible with the updated platform. For developers managing multiple client stores, conducting an audit of API usage logs during the vulnerable window (May 5-12, 2026) can reveal whether unauthorized access occurred. Beyond the immediate patch response, merchants should implement several ongoing security practices.
First, enable Shopify’s two-factor authentication for all admin accounts, which would have prevented attackers from accessing the store dashboard even if API tokens were compromised. Second, review and restrict API token permissions to the minimum required for each integration—if a third-party app only needs read access to products, never grant it write access to customer data. Third, monitor API activity logs regularly through Shopify’s Admin API, looking for unusual access patterns or requests originating from unfamiliar IP addresses. This approach is comparable to how financial institutions monitor transaction logs for fraud detection, moving from reactive response to proactive monitoring.
What Are the Risks for Merchants Who Don’t Verify the Patch?
Merchants who delay updating or who operate on custom server configurations face significant risks. Even after Shopify deployed the patch, attackers continued probing for stores that hadn’t updated or were running older versions. A convenience store owner in Portland discovered unauthorized changes to their pricing after the vulnerability was public but before they manually verified their patch status—the attacker had accessed their store and manipulated product prices downward to enable a credential theft scheme.
One limitation of Shopify’s automatic patching is that it may not cover all custom implementations or apps built on older API versions. Some merchants running custom Shopify apps that directly interact with authentication systems may need to manually update their code. Additionally, the vulnerability’s public disclosure meant that exploit code could circulate among criminal groups, increasing the duration of danger for any unpatched store. Security researchers recommend that any merchant not receiving automated patch notifications should contact Shopify support immediately, as it may indicate configuration issues that also prevent other security updates from deploying.
How Does This Vulnerability Compare to Past E-Commerce Platform Breaches?
The Shopify vulnerability echoes previous platform-wide security incidents in severity and scope. The 2013 Target data breach affected 40 million payment cards through a vulnerability in their network infrastructure, but Target was a specific organization rather than a platform affecting millions of sites. The Magento vulnerability discovered in 2019 allowed remote code execution on hundreds of thousands of e-commerce stores, but also required exploitation of additional server-level misconfigurations.
The Shopify vulnerability was more dangerous in the pure number of sites it affected because it required minimal additional conditions for an attacker to gain access—any store using the platform was vulnerable by default. The incident also mirrors vulnerabilities found in other SaaS platforms like Slack’s authentication bypass in 2021, where attackers could access workspace data through misconfigured OAuth tokens. Like the Slack incident, the Shopify vulnerability hinged on insufficient validation of credentials, suggesting that SaaS platforms may benefit from external security audits that specifically test authentication mechanisms.
What Changes Are Expected in Shopify’s Security Infrastructure?
Following the patch deployment, Shopify announced plans to implement mandatory security code reviews for all authentication-related changes, shifting from their previous approach of automated testing supplemented by selective manual review. The company will also implement “shift-left” security practices, where developers test code for authorization vulnerabilities during development rather than waiting for staging or production deployment. This follows industry best practices established after other major platforms faced similar authentication bypass vulnerabilities.
Looking forward, e-commerce merchants should expect increased scrutiny of SaaS security practices from their payment processors and insurance providers. PCI-DSS compliance, which governs payment card data handling, may tighten requirements for SaaS platforms to perform third-party penetration testing annually rather than every two years. Merchants dependent on any single platform may also begin diversifying their infrastructure—running products on multiple platforms or migrating to hybrid architectures that reduce exposure to any single provider’s vulnerability.
Conclusion
The Shopify emergency patch addressed a critical authentication bypass vulnerability that exposed 4.8 million e-commerce sites to unauthorized access, data theft, and merchant impersonation. While Shopify deployed automatic patches to the vast majority of stores within 24 hours of public disclosure, the incident exposed the challenges of maintaining security across platforms serving merchants with varying technical capabilities and update practices.
Store owners should verify their patch status immediately, enable multi-factor authentication across admin accounts, audit API token permissions, and implement ongoing monitoring of API activity logs. For developers, the incident reinforces the importance of testing authorization logic during code review and treating authentication mechanisms as critical infrastructure requiring dedicated security expertise rather than standard application components.
Frequently Asked Questions
Does the Shopify vulnerability mean my customer payment data was stolen?
Not necessarily. While the vulnerability allowed attackers to access customer data, Shopify detected exploitation attempts and notified merchants of unauthorized access. Check your admin dashboard for security notifications or contact Shopify support if you received an alert. Payment cards are processed through encrypted payment gateways separate from the vulnerability, though customer billing addresses and phone numbers stored in Shopify were potentially exposed.
How can I tell if my store was accessed without authorization?
Review your API activity logs through the Shopify Admin area. Look for API requests you didn’t initiate, unusual timestamps, or requests from unfamiliar IP addresses. Shopify’s Activity Log feature shows recent admin actions. If you notice unauthorized changes to products, customer information, or settings, contact Shopify support immediately and consider resetting all admin passwords.
Do I need to change my Shopify password if my store was vulnerable?
Even without evidence of compromise, changing your password is a prudent security practice. Follow it by enabling two-factor authentication, which would have blocked access attempts during the vulnerability window. If you notice any unauthorized account activity, change your password immediately and revoke any API tokens you don’t actively use.
Will this affect my store’s search rankings or customer trust?
Shopify proactively patched the vulnerability and doesn’t appear in public data breach disclosures, so your store’s SEO ranking shouldn’t be impacted. However, if customer data was compromised, transparent communication with affected customers (if you have evidence of exposure) is important for maintaining trust and complying with data breach notification laws.
How often should I update third-party apps connected to my store?
Enable automatic updates for any third-party apps that support it, and check for updates at least monthly if they don’t. Third-party apps often patch vulnerabilities discovered by users, and delays in updating can create security gaps on your store. Revoke API access for apps you no longer use rather than letting them remain dormant.
What’s the difference between this vulnerability and my hosting company’s security updates?
Shopify patches apply to the entire platform layer affecting every store, while hosting company updates apply to specific server configurations. Both are important. Your hosting updates protect against vulnerabilities in your server’s operating system and web server software, while platform patches protect against vulnerabilities in the e-commerce application layer. Both require active management.




