Building a secure PHP contact form requires a multi-layered approach that combines client-side validation with robust server-side checks, proper use of security tokens, and spam prevention mechanisms. A contact form that accepts unvalidated user input creates multiple attack vectors for hackers, including SQL injection, cross-site scripting, and spam bot abuse. The foundation of a secure contact form starts with server-side validation using PHP’s filter_var() function for email verification, POST method submission instead of GET to keep data hidden from browser URLs, and HTTPS encryption to protect data in transit.
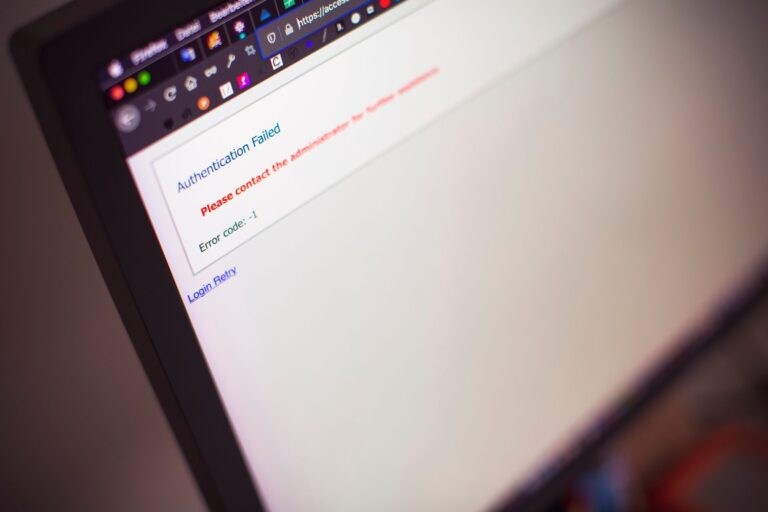
For example, a typical vulnerability occurs when developers rely solely on browser-level validation. A malicious actor can easily bypass client-side checks by disabling JavaScript or sending crafted requests directly to the server. A properly secured form validates every input on the server side, sanitizes all data, implements CSRF tokens stored in PHP sessions, uses techniques like the honeypot method to catch automated bot submissions, and applies rate limiting to prevent abuse. This article covers everything needed to build a contact form that protects your website, your users’ data, and your server from common security threats while maintaining a smooth user experience.
Table of Contents
- Why Server-Side Validation and Sanitization Matter More Than Client-Side Checks
- Implementing CSRF Token Protection to Prevent Cross-Site Request Forgery
- Spam Prevention Using Honeypot Fields and Google reCAPTCHA
- Rate Limiting and Session-Based Form Submission Intervals
- Using POST Method, HTTPS Encryption, and Secure Email Handling
- Building Responsive Forms With Bootstrap 5 and AJAX Submission
- Future-Proofing Your Contact Form With Modern Standards
- Conclusion
Why Server-Side Validation and Sanitization Matter More Than Client-Side Checks
Client-side validation provides immediate user feedback and improves the user experience by catching obvious errors before form submission. However, it offers zero security protection because JavaScript can be disabled, browser tools can be used to modify form data, or attackers can send requests directly to your server completely bypassing the front-end. This is why server-side validation is non-negotiable for any contact form handling real user data. Server-side validation in php should check every single field submitted to the server, regardless of what client-side validation passed. Use filter_var() with the FILTER_VALIDATE_EMAIL flag to properly validate email addresses according to RFC standards, which is far more reliable than regex patterns.
For other inputs, use appropriate filter functions and regular expressions to ensure data conforms to expected formats. Sanitize all text inputs with htmlspecialchars() or filter_sanitize_string() to prevent XSS attacks, and never trust any user input enough to use it directly in SQL queries. The critical limitation here is that even perfect server-side validation cannot prevent every attack. SQL injection, for instance, requires additional protection through prepared statements with parameterized queries. A contact form that validates “Bob@example.com” is a valid email does nothing to stop SQL injection if that validated email is then used in an unprotected database query. Always separate validation (checking data meets your requirements) from sanitization (removing dangerous characters) and parameterization (using safe database queries).
Implementing CSRF Token Protection to Prevent Cross-Site Request Forgery
CSRF (Cross-Site Request Forgery) attacks occur when an attacker tricks a user into submitting a form to your website from a malicious third-party site. The user may be logged in to your site in another browser tab, making their session valid, so the forged request executes with their credentials. CSRF tokens defeat this attack by requiring a secret token that only your legitimate form knows, making it impossible for a cross-site request to include the correct token. Implement CSRF protection by generating a unique token on the server using PHP sessions, embedding it as a hidden field in your contact form HTML, and validating that the submitted token matches the one stored in the session before processing the form. Generate tokens with random_bytes() and hash them with bin2hex() to create unpredictable values.
Store the original token in $_SESSION[‘csrf_token’] and require the submitted $_POST[‘csrf_token’] to match. If tokens don’t match, reject the form submission immediately. A common implementation mistake is reusing the same token for multiple form submissions. While convenient, this increases risk if a user’s session is somehow compromised. A more secure approach regenerates the token after each successful form submission. The downside is slightly increased complexity and the need to handle cases where users submit the form repeatedly in quick succession, but the security benefit is worth it for forms handling sensitive information.
Spam Prevention Using Honeypot Fields and Google reCAPTCHA
The honeypot technique works by adding a hidden form field to your HTML that real users won’t see or fill, but automated bots will. Bots scan HTML for input fields and fill them indiscriminately, so any submission with the honeypot field completed is definitely bot activity. Add an input field with display:none in CSS and a name like “website” or “phone” (fields bots expect), then reject any submission where this field contains data. Google reCAPTCHA v3 offers a more sophisticated approach by analyzing user behavior patterns to determine if a visitor is human. Unlike earlier versions that require users to click boxes or solve puzzles, v3 works silently in the background and returns a score between 0 and 1 indicating likelihood the action is legitimate.
Integrate reCAPTCHA v3 by adding the client-side script tag and sending the token returned from the client to your server, where you verify it against Google’s API using your secret key. Set a confidence threshold (typically 0.5 or higher) below which you reject the submission. The limitation of honeypot fields is they only catch simple bots; sophisticated attackers can detect and avoid honeypot fields. reCAPTCHA offers better protection but depends on Google’s service and sends user data to Google’s servers, which has privacy implications some users object to. Many sites use both methods together: the honeypot catches obvious automation, while reCAPTCHA catches sophisticated attacks, and legitimate users experience neither since both work invisibly.

Rate Limiting and Session-Based Form Submission Intervals
Rate limiting prevents a single user or IP address from submitting your contact form excessively, whether through accidental repeated clicks, deliberate spam attacks, or email harvesting. Implement session-based rate limiting by storing submission timestamps in $_SESSION, then checking if enough time has passed since the last submission before allowing a new one. A reasonable interval for contact forms is 60 seconds between submissions per session. To implement this, store the last submission timestamp in the session with $_SESSION[‘last_submission’] = time(), then before processing a new submission, check if (time() – $_SESSION[‘last_submission’] < 60). If the interval hasn't passed, display an error message asking the user to wait before submitting again.
This is transparent to legitimate users but prevents rapid-fire spam submissions. For forms handling sensitive data or money transfers, increase the interval to 300 seconds (5 minutes) or implement IP-based rate limiting on your web server using tools like fail2ban. The tradeoff with rate limiting is false positives: a legitimate user who accidentally submits twice in quick succession gets blocked. Communicate rate limiting clearly to users in error messages: “Please wait 45 seconds before submitting again.” Alternatively, implement smarter rate limiting that distinguishes between rapid successive submissions (likely accidental) and multiple different submissions across time (likely legitimate). This requires more code but provides better user experience.
Using POST Method, HTTPS Encryption, and Secure Email Handling
Always use the POST method for contact form submission instead of GET. GET requests include form data in the URL itself, which appears in browser history, server logs, referrer headers, and proxy caches. Any sensitive information like email addresses or messages becomes exposed in multiple places. POST requests send data in the request body where it’s not logged by default, though this still requires HTTPS to prevent network interception. HTTPS encryption is mandatory for any form handling user data. When a user submits a contact form over plain HTTP, attackers on the same network (public Wi-Fi, compromised routers, etc.) can intercept the submission and read every character.
HTTPS encrypts data in transit so only your server can decrypt it. Obtain an SSL certificate from Let’s Encrypt (free) or a commercial provider, configure your web server to redirect all HTTP requests to HTTPS, and test with tools like SSL Labs to verify proper configuration. Include HSTS headers (Strict-Transport-Security) to tell browsers to always use HTTPS for your domain. After validating and sanitizing the form submission, send emails using a dedicated library like PHPMailer rather than PHP’s mail() function. PHPMailer supports SMTP authentication, TLS encryption, and proper header handling, protecting emails in transit and during storage. Never embed user-submitted data directly into email headers, as attackers can inject newline characters to manipulate headers. The limitation of third-party email libraries is increased code complexity and dependency management, but the security benefits and reliability improvements justify the additional work.

Building Responsive Forms With Bootstrap 5 and AJAX Submission
Bootstrap 5 provides pre-built CSS classes for form styling that automatically adapt to mobile devices, ensuring your contact form looks professional on phones, tablets, and desktops without writing custom CSS. Wrap form elements in Bootstrap’s form-group and form-control classes, use validation feedback classes for error messages, and leverage Bootstrap’s grid system to organize fields in responsive columns. Enhance user experience by submitting forms asynchronously with JavaScript/AJAX instead of full page reloads.
When a user clicks submit, JavaScript sends the form data to your PHP script using fetch() or XMLHttpRequest, receives the response, and displays a success message without leaving the page. This feels faster and more modern than traditional form submission. Implement progressive enhancement so the form still works even if JavaScript is disabled (degrades to traditional submission), which is important for accessibility and users with JavaScript disabled.
Future-Proofing Your Contact Form With Modern Standards
The contact form landscape continues evolving with emerging standards like Web Authentication (WebAuthn) for optional user verification and JSON-LD structured data for contact information. While these remain optional for basic contact forms, awareness of development trends helps you plan upgrades.
The fundamentals—server-side validation, CSRF tokens, rate limiting, HTTPS, and proper email handling—remain essential and likely will for years. Looking forward, stay updated on PHP security practices through official documentation, maintain dependencies like PHPMailer through regular updates, and periodically audit your form handling code for vulnerabilities. Security isn’t a one-time implementation but an ongoing practice of staying informed about new threats and adapting defenses accordingly.
Conclusion
A secure PHP contact form requires multiple interconnected security layers working together: server-side validation using filter_var() and sanitization functions, CSRF tokens checked against sessions, honeypot fields and/or reCAPTCHA for spam prevention, rate limiting between submissions, POST method transmission over HTTPS, and secure email handling through PHPMailer. No single layer provides complete protection, but combining all these techniques creates a robust form that resists common attacks while remaining user-friendly.
Start by implementing the basics: moving validation to the server, adding CSRF token generation and validation, switching to POST with HTTPS, and using PHPMailer for emails. Then add spam prevention with honeypot fields or reCAPTCHA, implement rate limiting, and enhance the user interface with Bootstrap 5 and AJAX. Test your form thoroughly by attempting common attacks, and maintain security through regular updates and continued learning about new threats.